Blueprint: Build the Best in Cyber Defense
A weekly Technology podcast
Episodes of Blueprint
Mark All
Click here to send us your ideas and feedback on Blueprint!In this episode, we sit down with Rich Greene, a former United States Army Special Forces Green Beret and current SANS instructor for SEC275 and SEC301. Rich shares his incredible journ
Click here to send us your ideas and feedback on Blueprint!In this episode, we sit down with Ryan Thompson, a seasoned expert in building dashboards that actually detect real threats—not just look pretty. With experience at Elastic, Alert Logic
Click here to send us your ideas and feedback on Blueprint!Surprise!! It's a mini solo episode to kick off the new year and it's on one of the most important topics there is - how to achieve your goals in 2025 and beyond!In this episode I talk
Click here to send us your ideas and feedback on Blueprint!Mark Morowczynski returns for his 4th(!) time with his Microsoft coworker and identity and authentication expert Tarek Dawoud in this incredibly insightful conversation on the what, why
Click here to send us your ideas and feedback on Blueprint!In this episode, we take you behind the scenes of a complex gift card fraud investigation. Join host John Hubbard and guest Mark Jeanmougin as they explore the intricate details of unco
Click here to send us your ideas and feedback on Blueprint!In this mega-discussion with Seth Misenar on GenAI and LLM usage for security operations we cover some very interesting questions such as: - The importance of natural language processin
Click here to send us your ideas and feedback on Blueprint!Have you ever wondered what it takes to write and publish an information security book? In this special bonus episode following season 4, John discusses with Kathryn, Ingrid, and Carson
Click here to send us your ideas and feedback on Blueprint!"This final chapter of the book is no simple closer! "Turn Up the Volume by Expanding SOC Functionality" covers testing that your SOC is functioning as intended through activities such
Click here to send us your ideas and feedback on Blueprint!"Metrics, is there any more confusing and contentious topic in cybersecurity? In this episode the authors cover their advice and approach to measuring your team so that issues can be qu
Click here to send us your ideas and feedback on Blueprint!"Research has shown that communication is one of the most important factors for success in security incident response teams. In this chapter, the authors discuss the critical types of i
Click here to send us your ideas and feedback on Blueprint!Tool choice can be a make-or-break decision for security analysts, driving whether getting work done is a struggle, or an efficient, stress-free experience. How can we select the right
Click here to send us your ideas and feedback on Blueprint!In this special live recording from the SANS Blue Team Summit 2023, Kathryn Knerler, Ingrid Parker, and Carson Zimmerman joined John Hubbard they share their insights and expertise with
Click here to send us your ideas and feedback on Blueprint!There's no denying that the average security team is completely overwhelmed with options for data to collect. With a deluge of endpoint, network, and cloud data sources to collect, how
Click here to send us your ideas and feedback on Blueprint!Every security team has limited budget and time, how do you know where to focus? Cyber Threat Intelligence provides those answers! In this episode, Ingrid, Carson and Kathryn describe h
Click here to send us your ideas and feedback on Blueprint!No security team is perfect, so in this episode, authors Carson, Ingrid, and Kathryn discuss what it takes to prepare for fast, effective incident response capability. Covering preparat
Click here to send us your ideas and feedback on Blueprint!In this episode we dive deep on the "People" factor of the SOC. Who should you hire, what skills should you hire for, what backgrounds are most likely to lead to success for your team?
Click here to send us your ideas and feedback on Blueprint!In this episode we discuss how to decide on the right org structure and capabilities of your SOC. This includes questions like tiered vs. tierless models, which capabilities the SOC sho
Click here to send us your ideas and feedback on Blueprint!Though a SOC is responsible for protecting your organization's assets, it is not the owner of those systems. If the SOC is not established with a clear charter and authority to act, it
Click here to send us your ideas and feedback on Blueprint!As the saying goes, "If you don't know where you're going, any road will take you there!" - an approach that is disastrous to a SOC. In order to succeed, the SOC must have a clear under
Click here to send us your ideas and feedback on Blueprint!Welcome to a brand new season of Blueprint! In this intro episode we discuss "Fundamentals" chapter of the "11 Strategies of a World Class Cybersecurity Operations Center" with the auth
Click here to send us your ideas and feedback on Blueprint!Hello Blueprint listeners! We’re excited to announce that the release of season 4 of Blueprint is just around the corner, and we’ve got something very special cooked up for you. We’ve t
Click here to send us your ideas and feedback on Blueprint!Ever wonder how a cloud and application security expert views risks of cloud workloads? Well, wonder no more because on this episode we have Brandon Evans - SANS Certified Instructor an
Click here to send us your ideas and feedback on Blueprint!In this episode we speak with Joe Lykowski - Cyber Defense Lead at a major manufacturing company on what it takes to build a mature, transparent, and effective SOC. Joe brings years of
Click here to send us your ideas and feedback on Blueprint!Many of us are either looking to start a cyber security career, improve our knowledge and skills to further our career, or hire a team that has the most skilled and promising candidates
Click here to send us your ideas and feedback on Blueprint!In this episode of the Blueprint Podcast, we cover monitoring and securing macOS in an enterprise environment at scale with Jaron Bradley, Threat Detection lead at Jamf. We discuss the
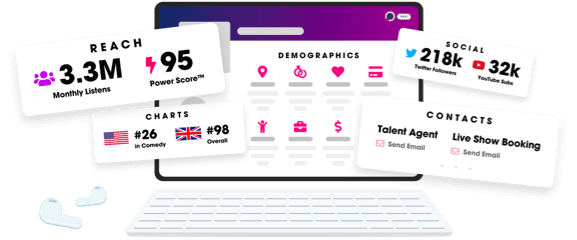
Unlock more with Podchaser Pro
- Audience Insights
- Contact Information
- Demographics
- Charts
- Sponsor History
- and More!
- Account
- Register
- Log In
- Find Friends
- Resources
- Help Center
- Blog
- API
Podchaser is the ultimate destination for podcast data, search, and discovery. Learn More
- © 2025 Podchaser, Inc.
- Privacy Policy
- Terms of Service
- Contact Us
