Security Breach
Episodes of Security Breach
Mark All
One of the great things about covering industrial cybersecurity is the number of reports, studies and white papers being produced right now to help provide intelligence on threats, research on new tools, and data on leading trends.The tough par
Endpoint security tools worked, but the hackers worked harder for their payday.While everyone likes to know how someone else might have screwed up and what the fallout looks like, the more import elements of episodes like this one come from the
We talk a lot about the growing complexity of hacking groups and how their tools and tactics continue to evolve. One such evolution is the ongoing specialization that runs rampant throughout the black hat community – especially when it comes to
Breaking down silos while securing the cloud and leveraging secure-by-design advancements.The challenges facing the industrial OT landscape that emanate from external sources are … varied, complex and constantly evolving. Smarter hacking groups
One of the goals of the show is to help you better understand all the threats facing your OT assets, your data and your people. In order to do that, we work to identify those individuals with a feel and in-depth understanding of these threats a
When we talk about the threat landscape for the industrial sector, the eye-catching, headline-grabbing hacking groups with nefarious names typically lead the list of concerns. And while understanding their well-publicized exploits are important
While we’re still in the infancy of 2025, the New Year has proven to have no issues in welcoming in a number of pre-existing challenges – whether we’re talking about cybersecurity or … other social topics.So, in continuing this trend, we tapped
The continued evolution of the CyberAv3ngers hacking group and its IIoT-focused malware.We talk a lot about change on Security Breach. Some of it’s good and obviously some of it makes us want to tear our hair out. Well, this episode, surprising
Winston Churchill famously stated that, “Those who fail to learn from history are doomed to repeat it.” His concerns about applying lessons learned to post WWII foreign policy initiatives rings just as true in the current cybersecurity climate.
As we begin to close out 2024 and look ahead to 2025, I couldn’t resist the urge to revisit some of my favorite guests from the last couple of months.While I’m grateful for everyone we’ve had on the show, and all the support we continue to rece
According to Fortinet’s 2024 State of Operational Technology and Cybersecurity Report, 43 percent of those surveyed reported a loss of business critical data or intellectual property so far in 2024– a number this is up nearly 10 percent from la
Next to artificial intelligence, one of the biggest buzz terms in industrial cybersecurity right now might be SBOM, or software bill of materials. The term generates equal parts concern and eye roll as those entrusted with enterprise defense lo
We assembled some "nerds from the basement" to cover a key strategy in combatting evolving threats.Today’s episode is going to take on a little different flavor, as we’re going to show you one particular tool that can impact a number of your se
For this episode, instead of tapping into one source for feedback and updates on industrial cybersecurity, we’re going to look at some of the key insights previous guests have offered on the evolving threat landscape – from increased risks eman
While there are plenty of unknowns when it comes to protecting the OT attack surface, there are some things that are undeniably true.We know that the frequency of attacks will continue to increase.We know that it’s not if your ICS will be probe
Maybe you’re sick of hearing about phishing schemes and the way hackers are using this strategy to infiltrate your networks, access intellectual data, shut down production, or hold your assets for ransom. If that’s the case, then you’ve made a
So, my daughters like to give me a hard time about growing old. Said another way, I’m a legacy asset - just like most of the devices many of you observe, manage and secure every day. Your machines are still in place because they work. While the
While the justifications for additional cybersecurity spending is easy to explain, getting buy-in at the C-level can be difficult. However, some recent research might help you win over those controlling the purse strings.SonicWall’s Mid-Year Cy
One of the most common topics we explore here on Security Breach is the ongoing challenge of asset visibility in the OT landscape. It's frustrating because it would seem that the solution starts with basic inventory management approaches, i.e.
According to Veeam’s 2024 Ransomware Trends Report, cyber victims stated that they were unable to restore 43 percent of whatever data was affected by ransomware attacks. This reaffirms what a number of Security Breach guests have stated about t
The ongoing theme in industrial cybersecurity centers on two competing dynamics – the desire to expand our implementation of automation and Industry 4.0 technologies with the goal of using more and faster connections, along with the decision-ma
We’re back to discuss an all-too-familiar topic – ransomware.Ironically enough, it seems the topics we describe in this manner become so familiar because we can’t figure out viable, long-term solutions. I think part of the challenge for industr
A smarter, well-funded hacker community means embracing basic, yet daunting cyber challenges.In manufacturing, regardless of your role, avoiding downtime is an obvious priority, and one of the motivating factors driving investments in cybersecu
Sophos recently reported that 65 percent of manufacturing and production organizations were hit by ransomware last year, which, unlike other sectors, is an increase. Overall, these attacks have increased by 41 percent for manufacturing since 20
I recently watched an interesting documentary called Turning Point: The Bomb and the Cold War on Netflix. Great watch – I’d highly recommend it. Essentially it positioned nearly every prominent geo-political event since World War II as fallout
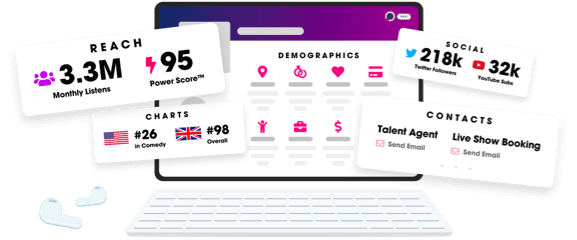
Unlock more with Podchaser Pro
- Audience Insights
- Contact Information
- Demographics
- Charts
- Sponsor History
- and More!
- Account
- Register
- Log In
- Find Friends
- Resources
- Help Center
- Blog
- API
Podchaser is the ultimate destination for podcast data, search, and discovery. Learn More
- © 2025 Podchaser, Inc.
- Privacy Policy
- Terms of Service
- Contact Us
